
Cross-border payment fraud is not a distant threat for European SMEs. 2024 EU/EEA fraud totaled €4.2B, with small and mid-sized businesses absorbing a disproportionate share of those losses. The pressure is real: regulators are tightening requirements, criminals are getting smarter, and the cost of a single compliance failure can derail months of growth. This guide walks you through a practical, four-stage framework covering risk assessment, process mapping, secure workflow design, and ongoing verification so your business can move money faster, stay compliant with PCI DSS and PSD2, and build the kind of payment trust that keeps partners and customers coming back.
Table of Contents
- Understand the risks and requirements
- Preparation: Map your current payment process
- Building a secure workflow: Step-by-step
- Verification and ongoing improvement
- Get compliant, secure, and efficient with Demivolt
- Frequently asked questions
Key Takeaways
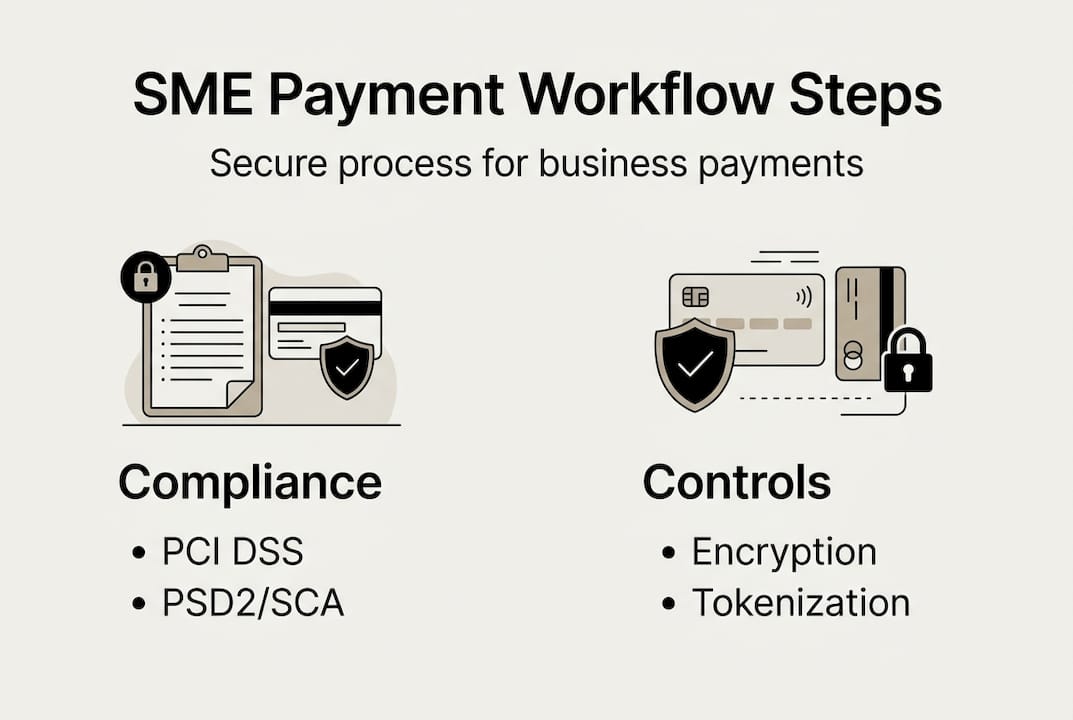
| Point | Details |
|---|---|
| Compliance is mandatory | PCI DSS and PSD2/SCA are essential for SME payment security and legal operations. |
| Real-time monitoring vital | Continuous monitoring and AI-driven checks greatly reduce fraud without adding friction. |
| Cross-border efficiency | Multi-currency and instant payment platforms cut costs and boost reliability for European SMEs. |
| Ongoing improvement pays off | Regular testing and updates are needed to stay ahead of evolving fraud threats. |
Understand the risks and requirements
Before you can fix a problem, you need to name it precisely. European SMEs operating across borders face a layered set of threats that go well beyond simple card fraud. Criminals target payment workflows at multiple points: intercepting credentials, exploiting weak approval chains, and manipulating employees through social engineering. Knowing which regulations govern each layer is the starting point for any serious security effort.
Here are the four compliance pillars every European SME payment workflow must address:
- PCI DSS: 12 core security requirements govern how cardholder data is stored, processed, and transmitted. Non-compliance exposes you to fines and card scheme penalties.
- PSD2 and SCA: The EU’s revised Payment Services Directive mandates Strong Customer Authentication (SCA) for electronic payments, requiring at least two independent verification factors.
- KYC/AML: Know Your Customer and Anti-Money Laundering rules require you to verify counterparty identities and monitor transactions for suspicious patterns.
- EU Instant Payments Regulation: Since 2024, euro instant payments must be offered at no extra cost, and payee IBAN verification is now mandatory before funds move.
“Cross-border payments for SMEs face fees up to 12x higher than domestic payments, compounded by delays, FX risks, and strict KYC/AML obligations.”
The table below maps the most common threats to the compliance layer that addresses each one:
| Threat | Compliance layer | Primary control |
|---|---|---|
| Card data theft | PCI DSS | Tokenization, encryption |
| Unauthorized transactions | PSD2/SCA | Multi-factor authentication |
| Money laundering | KYC/AML | Identity verification, monitoring |
| IBAN fraud | EU Instant Payments | Payee verification before transfer |
| FX manipulation | Internal controls | Multi-currency account segregation |
Understanding these layers lets you prioritize investment. Most SMEs underinvest in KYC/AML controls because they assume that is a bank’s job. It is not. If your business initiates or receives cross-border transfers, you share responsibility. Implementing workflow optimizations that address all four pillars simultaneously is far more efficient than patching each gap separately.
Preparation: Map your current payment process
With a clear understanding of risks and requirements, the next step is taking stock of your own processes so you know exactly where to focus. Most SMEs discover that their payment workflow was never formally designed. It evolved. That evolution creates blind spots.
Mapping your payment flow helps pinpoint weak points where fraud or noncompliance can occur. Start by documenting every step from trigger to settlement:
- Trigger: What initiates a payment? A purchase order, invoice approval, or subscription renewal?
- Data entry: Who enters payment details, and where are they stored?
- Verification: Is there a dual-approval step before funds move?
- Transfer and settlement: Which rails do you use? SEPA, SWIFT, card networks?
- Monitoring: Do you receive real-time alerts for unusual activity?
- Audit trail: Can you reconstruct every payment decision for a regulator within 24 hours?
Once you have this map, look for three specific failure patterns. First, single points of approval where one person can authorize and execute a payment without a second check. Second, unencrypted data storage, even temporary spreadsheets holding supplier IBANs. Third, access creep, where former employees or contractors still have system credentials.
Pro Tip: Run a tabletop exercise with your finance and operations teams. Simulate a fraudulent invoice scenario and trace exactly how far it would get in your current workflow before someone catches it. The answer is usually uncomfortable and always instructive.
Involve every internal stakeholder who touches payments: finance, procurement, IT, and any external accountants. Each person sees a different slice of the process. Only by combining those views do you get a complete picture. This preparation phase also makes it much easier to implement secure multi-currency payments later, because you already know which currency flows need the most attention.

Building a secure workflow: Step-by-step
Having mapped where your vulnerabilities lie, you are ready to follow a proven, evidence-based path to building a secure, compliant, and fast payment workflow. This is not about buying the most expensive software. It is about applying the right control at the right point in the process.
- Choose a PCI-compliant payment provider. Hosted payment pages and 3DS2 integration with dynamic exemptions reduce your PCI scope dramatically and enable secure SCA flows without building authentication infrastructure yourself.
- Secure every endpoint. Laptops, phones, and accounting software that connect to payment systems must run current OS versions, endpoint protection, and mandatory VPN for remote access.
- Implement role-based access control. No single user should have permission to both create and approve a payment. Separate these roles in your system settings and review them quarterly.
- Encrypt data in transit and at rest. Use TLS 1.3 for all payment data in motion. Tokenize stored card data so raw numbers never sit in your database.
- Enable SCA and 3DS2 for all card transactions. Configure dynamic exemptions carefully. Low-value and low-risk transactions can be exempted to reduce friction, but high-value cross-border payments should always trigger full authentication.
- Add real-time transaction monitoring. Set velocity rules: flag any payment that exceeds your average transaction value by more than 150%, or any new payee receiving a transfer above a defined threshold within 48 hours of being added.
- Use multi-currency accounts and SWIFT gpi. ISO 20022 data-rich transfers, TIPS instant payments, and multi-currency accounts are the key tools for secure, traceable cross-border workflows in 2026.
The comparison table below helps you match each workflow step to the right tool category:
| Workflow step | Recommended tool type | Key benefit |
|---|---|---|
| Card acceptance | Hosted payment page with 3DS2 | Reduced PCI scope, SCA compliance |
| Bank transfers | SEPA/SWIFT via regulated platform | Speed, traceability, compliance |
| FX risk management | Multi-currency account with rate lock | Predictable costs, no surprise losses |
| Identity verification | Integrated KYC provider | Automated AML screening |
| Monitoring | Real-time rules engine | Instant fraud alerts |
| Audit and reporting | ISO 20022 structured data | Regulator-ready records |
Pro Tip: Do not build your own payment page if you can avoid it. Every line of custom code that touches card data expands your PCI scope and your attack surface. Hosted pages from a regulated provider shift most of that liability and keep your secure payment workflow features lean and auditable.
Instant euro payments deserve special attention here. Since the EU Instant Payments Regulation took effect, your counterparties increasingly expect settlement in seconds, not days. Regulated platforms that support TIPS (TARGET Instant Payment Settlement) give you that speed while keeping every transaction inside a compliant, monitored environment.
Verification and ongoing improvement
Successfully building a secure workflow is only half the battle. Long-term success comes from continual validation and improvement. Threats evolve faster than most SME security policies do, and regulators expect you to keep pace.
Here is a practical verification cycle to run on a quarterly basis:
- Vulnerability scan: Run an automated scan of all systems that touch payment data. Document findings and remediate critical issues within 30 days.
- Access review: Pull a full list of users with payment permissions. Remove anyone who no longer needs access. Confirm role separation is still intact.
- Incident log review: Analyze every flagged transaction from the past quarter. Look for patterns: same payee, same time of day, same initiating user.
- Fraud rate benchmarking: Your target fraud rate should sit between 0.001% and 0.033% of transaction volume. Anything above that range signals a control gap.
- Policy update: If a new attack type emerged in the quarter, update your monitoring rules and staff training to address it.
Stat to watch: 2.8% of European business revenue is lost to fraud annually. AI risk scoring and velocity checks are the most effective tools for closing that gap.
SCA is powerful, but it is not a complete solution. SCA reduced fraud rates, yet threats like social engineering and Authorized Push Payment (APP) scams keep rising because they manipulate the legitimate payer rather than bypassing authentication. Criminals convince your finance manager to approve a fraudulent transfer voluntarily. No authentication layer stops that.
The answer is layered defense. Combine SCA with AI-powered risk scoring that flags behavioral anomalies, real-time monitoring that catches velocity spikes, and regular staff training that keeps your team skeptical of urgent payment requests. First-party fraud and refund abuse are also growing concerns in 2026, particularly for SMEs selling digital services across borders. Build refund approval workflows with the same rigor you apply to outbound payments. Use real-time monitoring features to catch patterns before they become losses.
Get compliant, secure, and efficient with Demivolt
Once you have your strategy, the right technology partner simplifies compliance, efficiency, and security in one place. Building a secure payment workflow from scratch is demanding, but you do not have to assemble a patchwork of disconnected tools to get there.
Demivolt is a regulated European fintech platform built specifically for SMEs that need business banking made clear without the complexity of traditional banking. The platform gives you dedicated IBAN accounts, SEPA and SWIFT payment management, multi-currency support, and real-time fraud controls under one compliant roof. Role-based user access, segregated client funds, and instant euro payment capability mean you can implement most of the workflow steps in this guide directly through Demivolt’s infrastructure. If your business is ready to move from a patched-together process to a purpose-built, audit-ready payment workflow, Demivolt is designed to get you there faster.
Frequently asked questions
What is the most critical compliance standard for SME payment security?
PCI DSS is the core requirement for protecting cardholder data, with 12 essential security controls that European SMEs must implement before processing any card payments.
How does SCA reduce payment fraud?
Strong Customer Authentication adds a second verification factor to electronic payments, which lowers fraud rates significantly, though it does not stop social engineering attacks where the legitimate payer is manipulated into approving a fraudulent transfer.
Which technologies help streamline secure cross-border payments?
ISO 20022, TIPS instant payments, and multi-currency accounts help SMEs reduce costs, improve traceability, and stay compliant with EU payment rules across borders.
How often should SME payment workflows be tested for vulnerabilities?
Secure workflows should be tested at least quarterly and immediately after any significant system change, as regular vulnerability testing is a direct PCI DSS requirement.